Today I’ll wrap up my series on Azure Active Directory’s (Azure AD) integration with Google’s G-Suite. In my first entry I covered the single-sign on (SSO) integration and in my second and third posts I gave an overview of Google’s Cloud Platform (GCP) and demonstrated how to access a G-Suite domain’s resources through Google’s APIs. In this post I’m going to cover how Microsoft provides automated provisioning of user, groups, and contacts . If you haven’t read through my posts on Google’s API (part 1, part 2) take a read through so you’re more familiar with the concepts I’ll be covering throughout this post.
SSO using SAML or Open ID Connect is a common capability of most every cloud solutions these days. While that solves the authentication problem, the provisioning of users, groups, and other identity-relates objects remains a challenge largely due to the lack of widely accepted standards (SCIM has a ways to go folks). Vendors have a variety of workarounds including making LDAP calls back to a traditional on-premises directory (YUCK), supporting uploads of CSV files, or creating and updating identities in its local databases based upon the information contained in a SAML assertion or Open ID Connect id token. A growing number of vendors are exposing these capabilities via a web-based API. Google falls into this category and provides a robust selection of APIs to interact with its services from Gmail to resources within Google Cloud Platform, and yes even Google G-Suite.
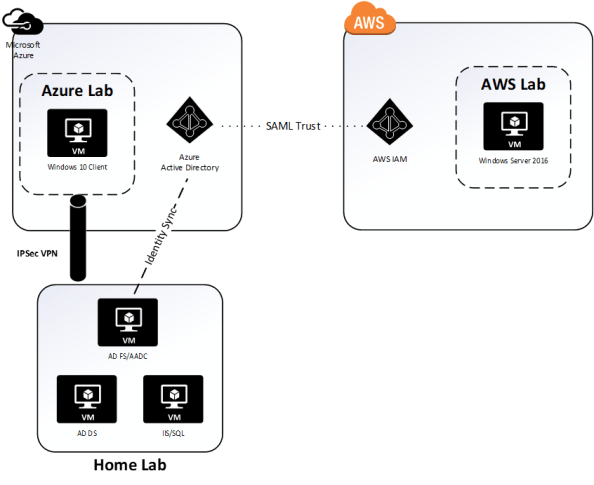
If you’re a frequent user of Azure AD, you’ll have run into the automatic provisioning capabilities it brings to the table across a wide range of cloud services. In a previous series I covered its provisioning capabilities with Amazon Web Services. This is another use case where Microsoft leverages a third party’s robust API to simplify the identity management lifecycle.
In the SSO Quickstart Guide Microsoft provides for G-Suite it erroneously states:
“Google Apps supports auto provisioning, which is by default enabled. There is no action for you in this section. If a user doesn’t already exist in Google Apps Software, a new one is created when you attempt to access Google Apps Software.”
This simply isn’t true. While auto provisioning via the API can be done, it is a feature you need to code to and isn’t enabled by default. When you enable SSO to G-Suite and attempt to access it using an assertion containing the claim for a user that does not exist within a G-Suite domain you receive the error below.
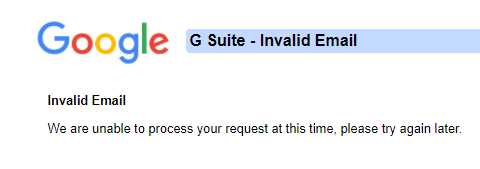
This establishes what we already knew in that identities representing our users attempting SSO to G-Suite need to be created before the users can authenticate. Microsoft provides a Quickstart for auto provisioning into G-Suite. The document does a good job telling you were to click and giving some basic advice but really lacks in the detail into what’s happening in the background and describing how it works.
Let’s take a deeper look shall we?
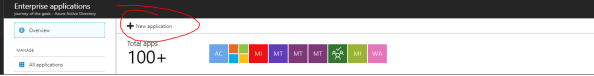
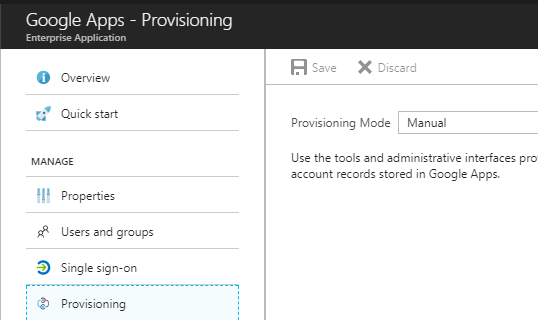
If you haven’t already, add the Google Apps application from the Azure AD Application Gallery. Once the application is added navigate to the blade for the application and select the Provisioning page. Switch the provisioning mode from manual to automatic.
Right off the bat we see a big blue Authorize button which tells us that Microsoft is not using the service accounts pattern for accessing the Google API. Google’s recommendation is to use the service account pattern when accessing project-based data rather than user specific data. The argument can be made that G-Suite data doesn’t fall under project-based data and the service account credential doesn’t make sense. Additionally using a service account would require granting the account domain-wide delegation for the G-Suite domain allowing the account to impersonate any user in the G-Suite domain. Not really ideal, especially from an auditing perspective.
By using the Server-side Web Apps pattern a new user in G-Suite can be created and assigned as the “Azure AD account”. The downfall with of this means you’re stuck paying Google $10.00 a month for a non-human account. The price of good security practices I guess.
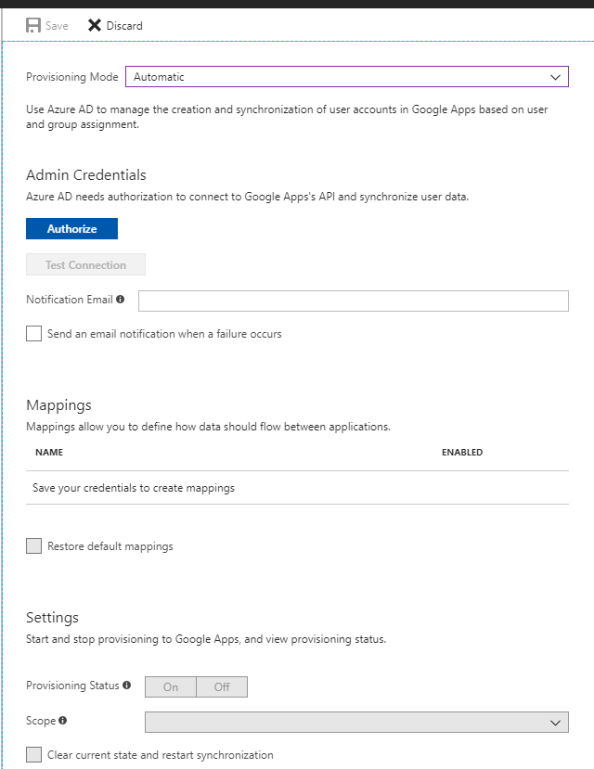
Microsoft documentation states that the account must be granted the Super Admin role. I found this surprising since you’re effectively giving the account god rights to your G-Suite domain. It got me wondering what authorization scopes is Microsoft asking for? Let’s break out Fiddler and walk through the process that kicks off after clicking on the Authorization button.
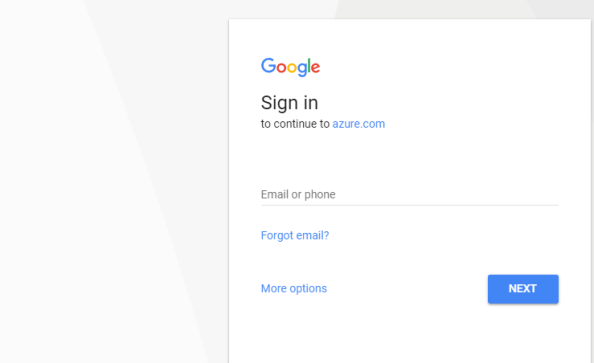
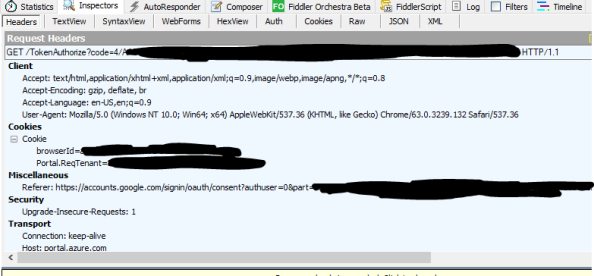
A new window pops up from Google requesting me to authenticate. Here Azure AD, acting as the OAuth client, has made an authorization request and has sent me along with the request over to the Google which is acting as the authorization server to authenticate, consent to the access, and take the next step in the authorization flow.
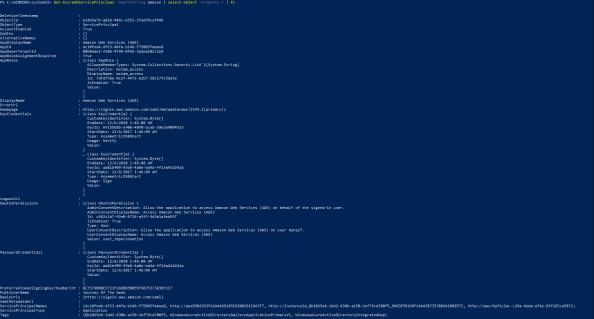
When I switch over to Fiddler I see a number of sessions have been captured. Opening the WebForms window of the first session to accounts.google.com a number of parameters that were passed to Google.
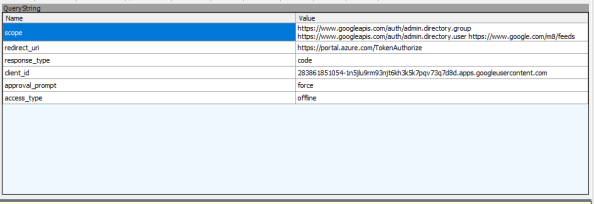
The first parameter gives us the three authorization scopes Azure AD is looking for. The admin.directory.group and admin.directory.user are scopes are both related to the Google Directory API, which makes sense if it wants to manage users and groups. The /m8/feeds scope grants it access to manage contacts via the Google Contacts API. This is an older API that uses XML instead of JSON to exchange information and looks like it has been/is being replaced by the Google People API.
Management of contacts via this API is where the requirement for an account in the Super Admin role originates. Google documentation states that management of domain shared contacts via the /m8/feeds API requires an administrator username and password for Google Apps. I couldn’t find any privilege in G-Suite which could be added to a custom Admin role that mentioned contacts. Given Google’s own documentation along the lack of an obvious privilege option, this may be a hard limitation of G-Suite. Too bad too because there are options for both Users and Groups. Either way, the request for this authorization scope drives the requirement for Super Admin for the account Azure AD will be using for delegated access.
The redirect_uri is the where Google sends the user after the authorization request is complete. The response_type tells us Azure AD and Google are using the OAuth authorization code grant type flow. The client_id is the unique identifier Google has assigned to Azure AD in whatever project Microsoft has it built in. The approval_prompt setting of force tells Google to display the consent window and the data Azure AD wants to access. Lastly, the access_type setting of offline allows Azure AD to access the APIs without the user being available to authenticate via a refresh token which will be issued along with the access token. Let’s pay attention to that one once the consent screen pops up.
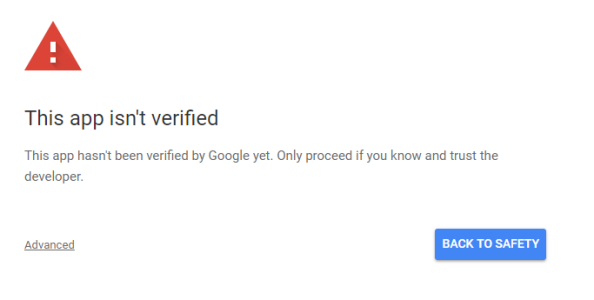
I plug in valid super user credentials to my G-Suite domain and authenticate and receive the warning below. This indicates that Microsoft has been naughty and hasn’t had their application reviewed by Google. This was made a requirement back in July of 2017… so yeah… Microsoft maybe get on that?
To progress to the consent screen I hit the Advanced link in the lower left and opt to continue. The consent window then pops up.
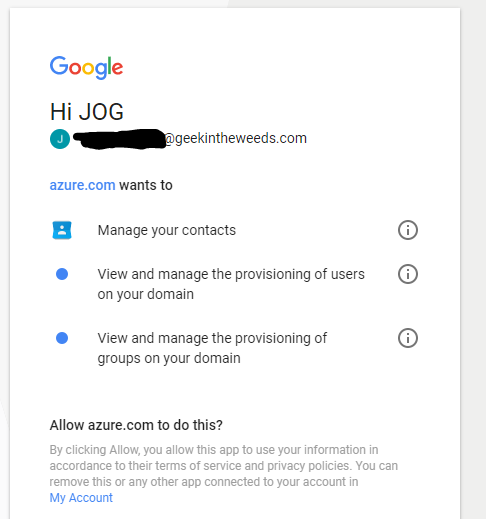
Here I see that Microsoft has registered their application with a friendly name of azure.com. I’m also shown the scopes that the application wants to access which jive with the authorization scopes we saw in Fiddler. Remember that offline access Microsoft asked for? See it mentioned anywhere in this consent page that I’m delegating this access to Microsoft perpetually as long as they ask for a refresh token? This is one of my problems with OAuth and consent windows like this. It’s entirely too vague as to how long I’m granting the application access to my data or to do things as me. Expect to see this OAuth consent attacks continue to grow in in use moving forward. Why worry about compromising the user’s credentials when I can display a vague consent window and have them grant me access directly to their data? Totally safe.
Hopping back to the window, I click the Allow button and the consent window closes. Looking back at Fiddler I see that I received back an authorization code and posted it back to the reply_uri designated in the original authorization request.
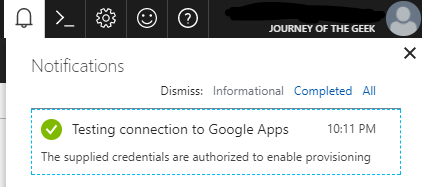
Switching back to the browser window for the Azure Portal the screen updates and the Test Connection button becomes available. Clicking the button initiates a quick check where Azure AD obtains an access token for the scopes it requires unseen to the user. After the successful test I hit the Save button.
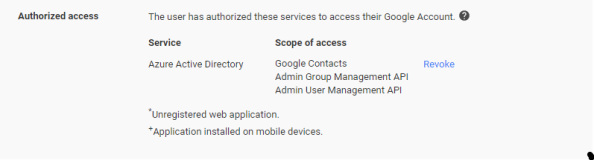
Switching to the browser window for the Google Admin Portal let’s take a look at the data that’s been updated for the user I used to authorize Microsoft its access. For that I select the user, go to the Security section and I now see that the Azure Active Directory service is authorized to the contacts, user, and group management scopes.
Switching back to the browser window for the Azure Portal I see some additional options are now available.
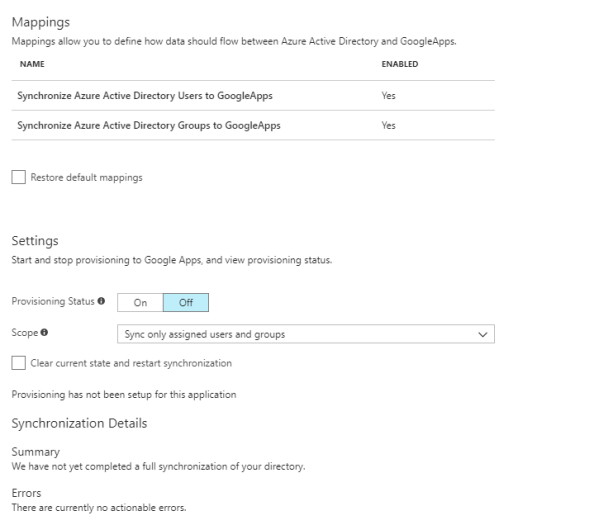
The mappings are really interesting and will look familiar to you if you’ve ever done anything with an identity management tool like Microsoft Identity Manager (MIM) or even Azure AD Sync. The user mappings for example show which attributes in Azure AD are used to populate the attributes in G-Suite.
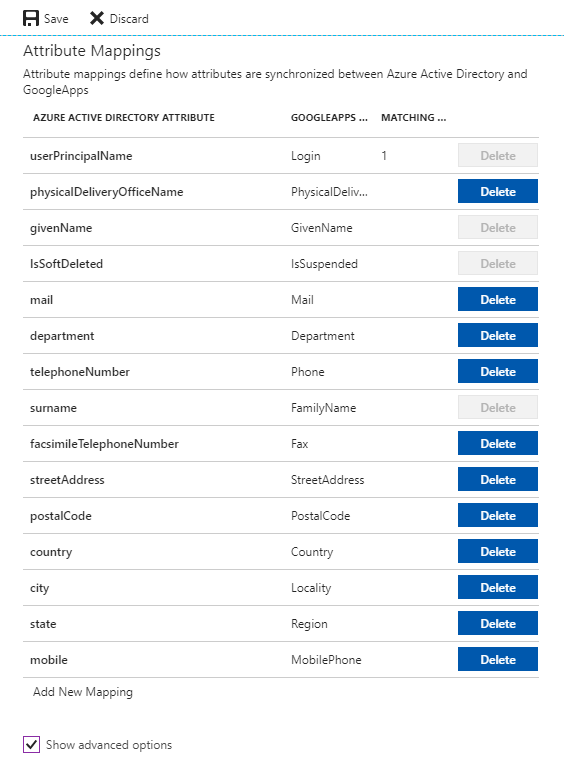
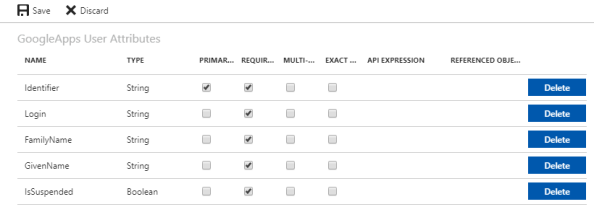
The attributes that have the Delete button grayed out are required by Google in order to provision new user accounts in a G-Suite domain. The options available for deletion are additional data beyond what is required that Microsoft can populate on user accounts it provisions into G-Suite. Selecting the Show advanced options button, allow you to play with the schema Microsoft is using for G-Suite. What I found interesting about this schema is it doesn’t match the resource representation Google provides for the API. It would have been nice to match the two to make it more consumable, but they’re probably working off values used in the old Google Provisioning API or they don’t envision many people being nerdy enough to poke around the schema.
Next up I move toggle the provisioning status from Off to On and leave the Scope option set to sync only the assigned users and groups.
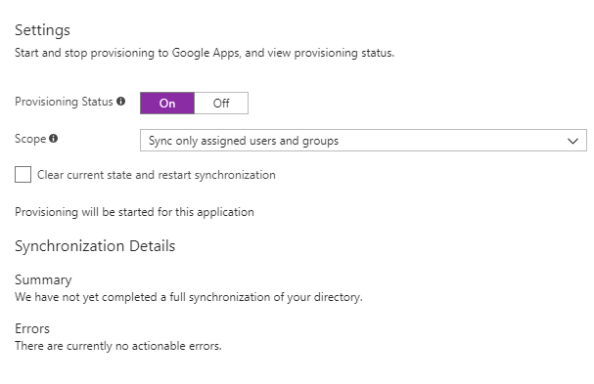
I then hit the Save button to save the new settings and after a minute my initial synchronization is successful. Now nothing was synchronized, but it shows the credentials correctly allowed Azure AD to hit my G-Suite domain over the appropriate APIs with the appropriate access.
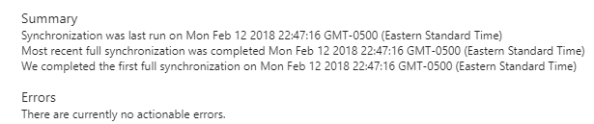
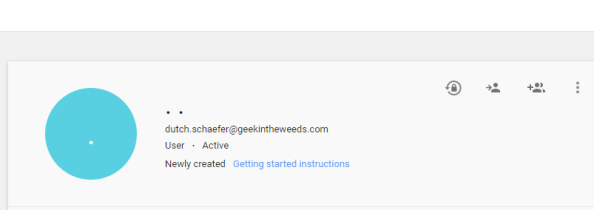
So an empty synchronization works, how about one with a user? I created a new user named dutch.schaefer@geekintheweeds.com with only the required attributes of display name and user principal name populated, assigned the new user to the Google Apps application and give Azure AD a night to run another sync. Earlier tonight I checked the provisioning summary and verified the sync grabbed the new user.
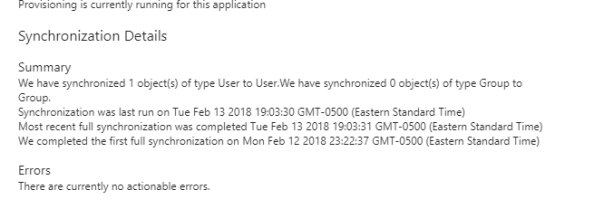
Review of the audit logs for the Google Apps application shows that the new user was exported around 11PM EST last night. If you’re curious the synch between Azure AD and G-Suite occurs about every 20 minutes.
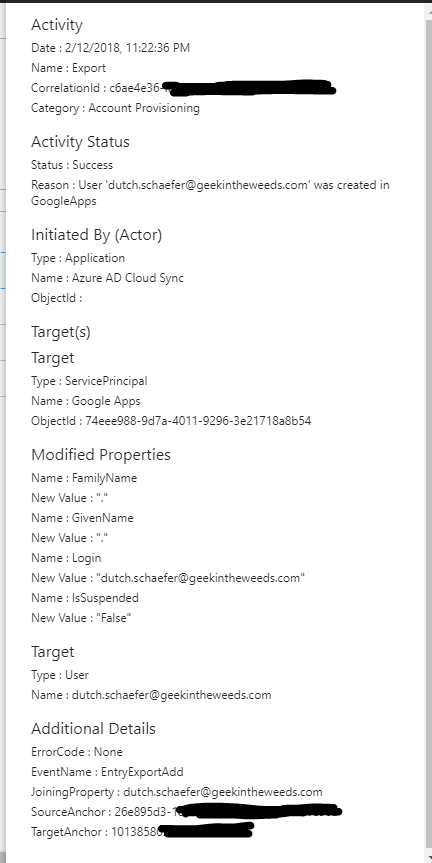
Notice that the FamilyName and GivenName attributes are set to a period. I never set the first or last name attributes of the user in Azure AD, so both attributes are blank. If we bounce back to the attribute mapping and look at the attributes for Google Apps, we see that FamilyName and GivenName are both required meaning Azure AD had to populate them with something. Different schemas, different requirements.
Switching over to the Google Admin Console I see that the new user was successfully provisioned into G-Suite.
Pretty neat overall. Let’s take a look at what we learned:
- Azure AD supports single sign-on to G-Suite via SAML using a service provider-initiated flow where Azure AD acts as the identity provider and G-Suite acts as the service provider.
- A user object with a login id matching the user’s login id in Azure Active Directory must be created in G-Suite before single sign-on will work.
- Google provides a number of libraries for its API and the Google API Explorer should be used for experimentation with Google’s APIs.
- Google’s Directory API is used by Azure AD to provision users and groups into a G-Suite domain.
- Google’s Contacts API is used by Azure AD to provision contacts into a G-Suite domain.
- A user holding the Super Admin role in the G-Suite domain must be used to authorize Azure AD to perform provisioning activities. The Super Admin role is required due to the usage of the Google Contact API.
- Azure AD’s authorization request includes offline access using refresh tokens to request additional access tokens to ensure the sync process can be run on a regular basis without requiring re-authorization.
- Best practice is to dedicate a user account in your G-Suite domain to Azure AD.
- Azure AD uses the Server-side Web pattern for accessing Google’s APIs.
- The provisioning process will populate a period for any attribute that is required in G-Suite but does not have a value in the corresponding attribute in Azure AD.
- The provisioning process runs a sync every 20 minutes.
Even though my coding is horrendous, I absolutely loved experimenting with the Google API. It’s easy to realize why APIs are becoming so critical to a good solution. With the increased usage of a wide variety of products in a business, being able to plug and play applications is a must. The provisioning aspect Azure AD demonstrates here is a great example of the opportunities provided when critical functionality is exposed for programmatic access.
I hope you enjoyed the series, learned a bit more about both solutions, and got some insight into what’s going on behind the scenes.