Welcome back fellow geeks! I hope you managed to have an enjoyable holiday and took a break from the grind. I took a good week off, and minus some reading around AKS (Azure Kubernetes Service), I completely shut off the work and tech side of my brain. It was a great change!
Today I am back with a new entry into my What If series. In this entry I’ll be covering an interesting quirk of ASR (Azure Site Recovery) that I ran into helping a customer test out the service. For those of you unfamiliar with ASR, it’s a managed service in Microsoft Azure that provides business continuity and disaster recovery for VMs (virtual machines) both within Azure and on-premises. It can also be used to when migrating VMs from on-premises to Azure, between regions, or between availability zones.
With the quick introduction to the service out of the way, let’s get to it.
What if I wanted to test Azure Site Recovery with both Windows and Linux virtual machines?
Over the holiday break I received an email from a customer who doing some validation testing for a planned migration for ADE (Azure Disk Encryption) to SSE (Server-Side Encryption) for Managed Disks using a CMK (Customer Managed Key). As part of the validation process, the customer wanted to understand how ASR would work after when using SSE with CMK instead of ADE. The customer was making the shift from ADE to SSE for Managed Disks with CMK for a few reasons including:
- Performance benefits by shifting the encryption engine out of the operating system
- No limitations on specific images for the virtual machine
- No VM extensions required
- Can be combined with host-based encryption for end to end encryption
The customer followed the instructions on how to set up ASR for SSE with CMK-enabled disks referenced here. Replication was successful but they noticed the data disk they had attached to the VM in the source region was not automatically attached to the VM in the destination region and required manual attachment. While an inconvenience for a single test, this could create a huge headache at scale when you’re talking about hundreds of VMs.
After receiving the email I immediately spun up a very simple environment in Azure in the East US 2 region consisting of a single virtual network, Windows VM with an attached data disk, Azure Key Vault instance with a single key, and a disk encryption set. In the Central US region I created a second virtual network, Azure Key Vault instance with a single key, and a disk encryption set. My plan was to fail the VM over from East US 2 to Central US using ASR.

As I went through the enablement process I ensured both the OS disk and the data disk were selected for replication as seen in the image below.
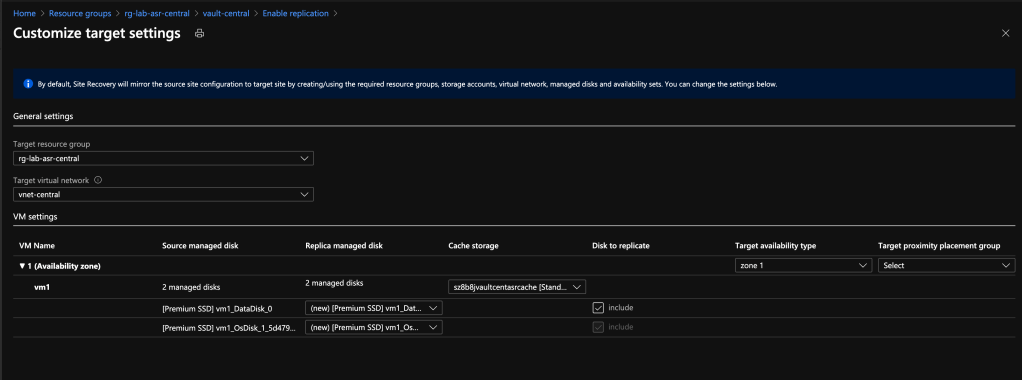
Reviewing the configuration shows that two managed disks are set to replicate.
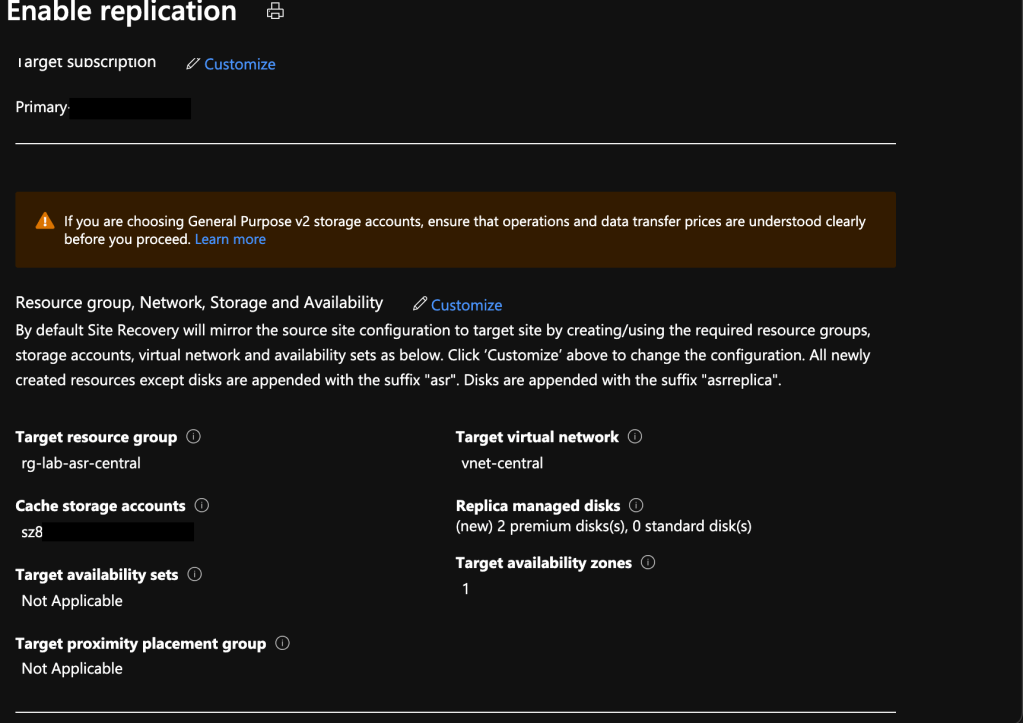
After confirmation I left it alone and came back an hour later and checked the destination resource group. Replicas of both managed disks are present in the destination resource group. Good so far.

I then did a test failover and pulled up the VM and observed the same thing my customer did. The data disk was not attached even though it was replicated. I was able to manually attach it without an issue, but again, how does this work at scale? Even more interesting was the status of the VM in the Site Recovery section of the Recovery Services Vault. It did not show the data disk as being replicated.
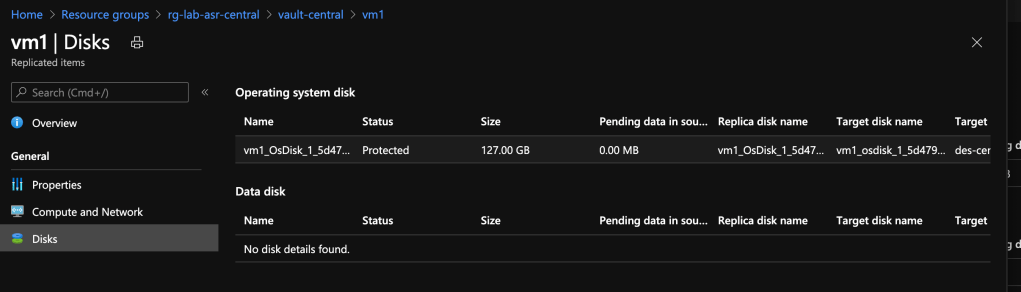
I ran through the same process a few more times and ran into the same result each time. To make sure it wasn’t an issue with the information the portal was displaying, I wrote some quick Python code to hit the replicationprotecteditem endpoint within the ARM REST API. The results from the API also included only the OS disk in the replication status.
Was this a bug? Did both the customer and I mess something up in setting this up? Turns out it was neither. This is actually expected behavior when replicating a Windows VM when a data disk is attached that is uninitialized in the OS (operating system). For you young folks out there that have never initialized a disk in Microsoft Windows or those of you don’t spend much time in Windows, initialization consists of creating the partition table on the drive which must occur prior formatting the partition with a file system. So why is this required? I’m not really sure and can only theorize. A friend and I talked this over and we theorize it may be a requirement to ensure the disk has some unique identifier in the operating system which may not be able to be generated without the disk first being partitioned.
Note that this issue only occurs with Windows VMs with an uninitialized data disk. It does not occur if the disk has been initialized in Windows and does not occur at all with a Linux VM whether the disk has been partitioned or not. In those cases the data disk will be attached after the VM is failed over.
So there you go folks. If you decide to test out ASR for a proof-of-concept or just a learning experience, remember to initialize your disks on your Windows VMs!
See you next post!
Hello Matt, how are you?
I hope you are fine. I benefit a lot from your articles. Therefore, thank you very much.
Stay healthy, Greetings from Turkey!
LikeLike
Doing great and hope you are as well!
I’m thrilled to hear you are getting value from my ramblings. It is a huge motivator to know this information is helping others!
Stay safe and have a wonderful 2021!
LikeLike
Thanks, there is a warning on my portal that AIP will not be managed on the portal after March 2021. Do you have any information on this subject? What should I do?
LikeLiked by 1 person
It’s been a long time since I’ve done anything with AIP, but if I had to hazard a guess, it sounds like you might be using classic labels still. Check out this https://docs.microsoft.com/en-us/azure/information-protection/faqs#whats-the-difference-between-the-azure-information-protection-classic-and-unified-labeling-clients
LikeLiked by 1 person
Thank you for your support, I have another question, I will be glad if it helps. By the way, I’m a super noob.
Is it possible to integrate Titus with Azure RMS? Classification should be Titus, protection is Azure RMS.
LikeLiked by 1 person
Not sure on that. I could have sworn that I’ve heard of the integration, but unfortunately I haven’t done much with Azure RMS for a few years now.
LikeLiked by 1 person
Hahaha, you are rock!
Thank you for your support and wish you a lifetime of happiness.
LikeLiked by 2 people