Today I’ll continue my deep dive into AWS Managed Microsoft AD. In the last blog post I provided an overview of the reasons an organization would want to explore a managed service for Windows Active Directory (Windows AD). In this post I’ll be providing an overview of my lab environment and demoing how to setup an instance of AWS Managed Microsoft AD and seamlessly joining a Windows EC2 instance.
Let’s dive right into it.
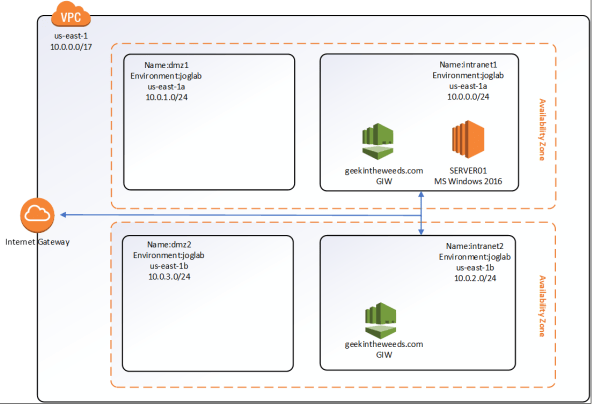
Let’s first cover what I’ll be using as a lab. Here I’ve setup a virtual private cloud (VPC) with default tenancy which is a requirement to use AWS Managed Microsoft AD. The VPC has four subnets configured within it named intranet1, intranet2, dmz1, and dmz2. The subnets intranet1/dmz1 and intranet2/dmz2 provide us with our minimum of two availability zones, which is another requirement of the service. I’ve created a route table that routes traffic destined for IP ranges outside the VPC to an Internet Gateway and applied that route table to both the intranet1 and intranet2 subnets. This will allow me to RDP to the EC2 instances I create. Later in the series I’ll configure VPN connectivity with my on-premises lab to demonstrate how the managed AD can be used on-prem. Below is a simple Visio diagraming the lab.
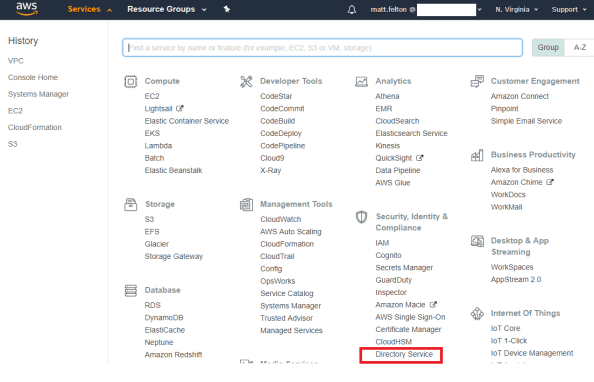
To create a new instance of AWS Managed Microsoft AD, I’ll be using the AWS Management Console. After successfully logging in, I navigate to the Services menu and select the Directory Service link under the Security, Identity & Compliance section as seen below.
The Directory Service page then loads which is a launching pad for configuration of the gamut of AWS Directory Services including AWS Cloud Directory, Simple AD, AD Connector, Amazon Cognito, and of course AWS Managed Microsoft AD. Any directory instance that you’ve created would appear in the listing to the right. To create a new instance I select the Set up Directory button.

The Set up a directory page loads and I’m presented with the options to create an instance of AWS Managed Microsoft AD, Simple AD, AD Connector, or an Amazon Cognito User Pool. Before I continue, I’ll provide the quick and dirty on the latter three options. Simple AD is actually Samba made to emulate some of the capabilities of Windows Active Directory. The AD Connector acts as a sort of proxy to interact with an existing Windows Active Directory. I plan on a future blog series on that one. Amazon Cognito is Amazon’s modern authentication solution (looks great for B2C) providing Open ID Connect, OAuth 2.0, and SAML services to applications. That one will warrant a future blog series as well. For this series we’ll be select the AWS Managed Microsoft AD option and clicking the Next button.

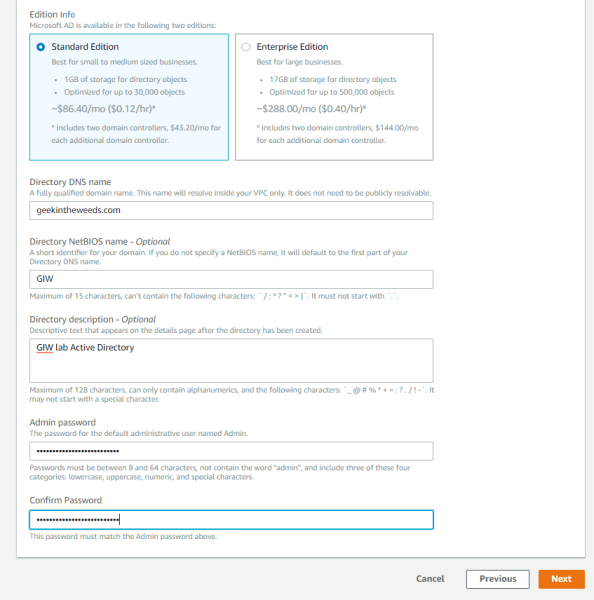
A new page loads where we configure the directory information. Here I’m given the option to choose between a standard or enterprise offering of the service. Beyond storage I’ve been unable to find or pull any specifications of the EC2 instances Amazon is managing in the background for the domain controllers. I have to imagine Enterprise means more than just 16GB of storage and would include additional memory and CPU. For the purposes of this series, I’ll be selecting Standard Edition.
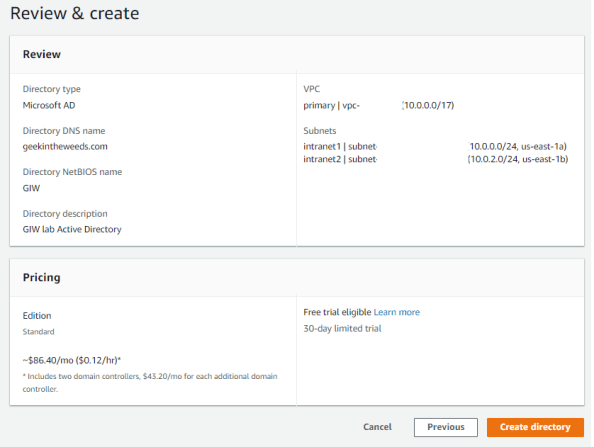
Next I’ll provide the key configuration details for forest which includes the fully qualified domain name (FQDN) for the forest I want created as well as optionally specifying the NetBIOS name. The Admin password set here is used for the delegated administrator account Amazon creates for the customer. Make sure this password is securely stored, because if it’s lost Amazon has no way of recovering it.
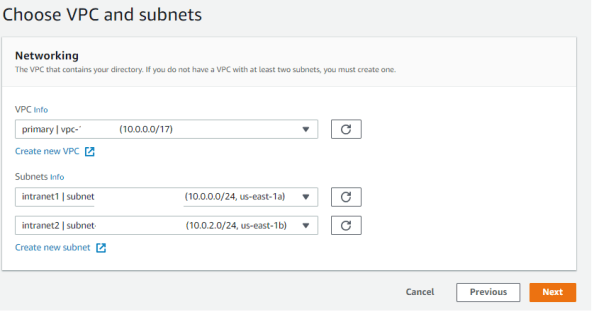
After clicking the Next button I’m prompted to select the virtual private cloud (VPC) I want to service deployed to. The VPC used must include at least two subnets that are in different availability zones. I’ll be using the intranet1 and intranet2 subnets shown in my lab diagram earlier in the post.
The next page that loads provides the details of the instance that will be provisioned. Once I’m satisfied the configuration is correct I select the Create Directory button to spin up the service.
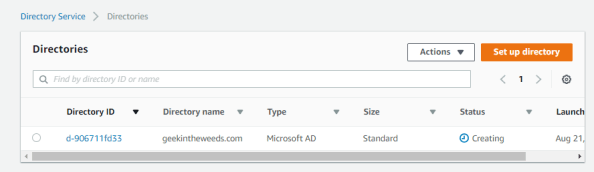
Amazon states it takes around 20 minutes or so to spin up the instance, but my experience was more like 30-45 minutes. The main Directories Services page displays the status of the directory as Creating. As part of this creation a new Security Group will be created which acts as a firewall for the managed domain controllers. Unlike some organization that try to put firewalls between domain-join clients and domain controllers, Amazon has included all the necessary flows and saves you a ton of troubleshooting with packet captures.
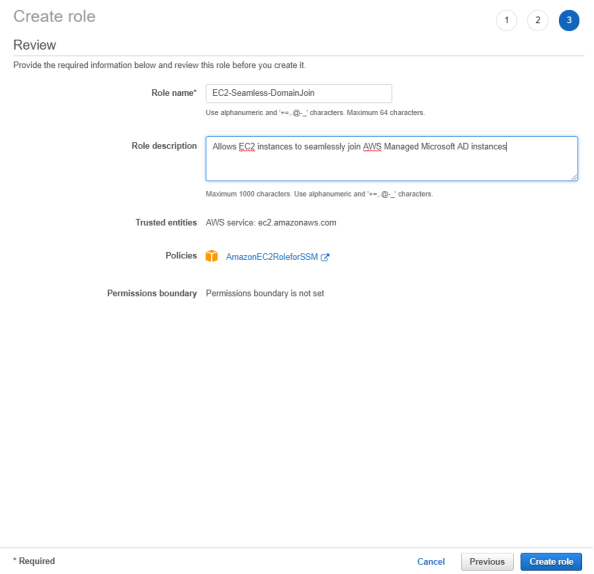
One of the neat features offered with this service is the ability to seamlessly domain-join Windows EC2 instances during creation. Before that feature can be leveraged an AWS Identity and Access Management (IAM) role needs to setup that has the AmazonEC2RoleforSSM attached to it. AWS IAM is by far my favorite feature of AWS. At a very high level, you can think of AWS IAM as being the identity service for the management of AWS resources. It’s insanely innovative and flexible in its ability to integrate with modern authentication solutions and in how granular you can be in defining rights and permissions to AWS resources. I could do multiple series just covering the basics (which I plan to do in the future) but to progress this entry let me briefly explain AWS IAM Roles. Think of an AWS IAM Role as a unique security principal similar to a user but without any credentials. The role is assigned a set of rights and permissions which AWS refers to as a policy. The role is then assumed by a human (such as federated user) or non-human (such as EC2 instance) granting the entity the rights and permissions defined in the policy attached to the role. In this scenario the EC2 instance I create will be assuming the AmazonEC2RoleforSSM. This role grants a number of rights and permissions within AWS’s Simple System Manager (SSM), which for your Microsoft-heavy users is a scaled down SCCM. It requires this role to orchestrate the domain-join upon instance creation.
To create the role I’ll open back up the Services menu and select IAM from the Security, Identity & Compliance menu.

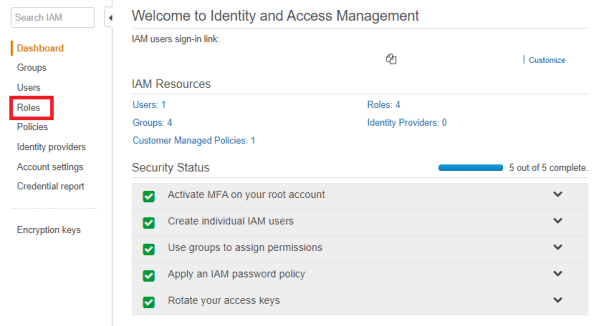
The IAM dashboard will load which provides details as to the number of users, groups, policies, roles, and identity providers I’ve created. From the left-hand menu I’ll select the Roles link.
The Role page then loads and displays the Roles configured for my AWS account. Here I’ll select the Create Role button to start the role creation process.

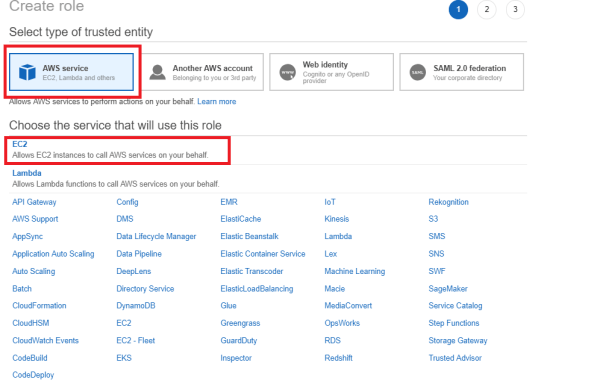
The Create Role page loads and prompts me to select a trusted entity type. I’ll be using this role for EC2 instances so I’ll select the AWS service option and chose EC2 as the service that will use the role. Once both options are selects I select the Next: Permission button.
Next up we need to assign a policy to the role. We can either create a new policy or select an existing one. For seamless domain-join with AWS Managed Microsoft AD, EC2 instances must use the AmazonEC2forSSM policy. After selecting the policy I select the Next: Review button.

On the last page I’ll name the role, set a description, and select the Create role button. The role is then provisioned and available for use.
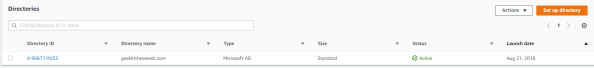
Navigating back to the Directory Services page, I can see that the geekintheweeds.com instance is up and running. This means we can now create some EC2 instances and seamlessly join them to the domain.
The EC2 instance creation is documented endless on the web, so I won’t waste time walking through it beyond showing the screenshot below which displays the options for seamless domain-join. The EC2 instance created will be named SERVER01.

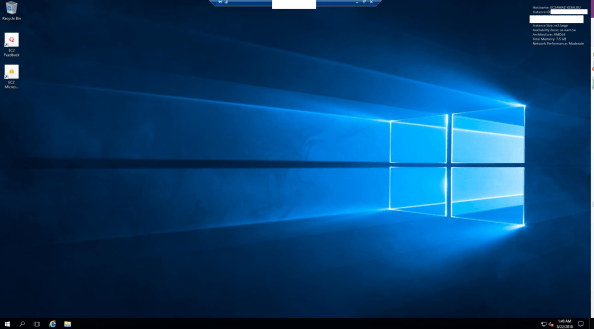
After a few minutes the instance is ready to go. I start the Remote Desktop on my client machine and attempt a connection to the EC2 instance using the Admin user and credentials I set for the AD domain.

Low and behold I’m logged into the EC2 instance using my domain credentials!
As you can see setup of the service and EC2 instances is extremely simple and could made that much more simple if we tossed out the GUI and leveraged cloud formation templates to seamlessly spin up entire environments at a push of a button.
We covered a lot of content in this entry so I’ll close out here. In the next entry I’ll examine the directory structure Amazon creates including the security principals and key permissions.
See you next post!
