Today I continue my series of blog posts where I take a look behind the curtains at the Microsoft “magic” behind Azure Active Directory. In the previous posts I broke down the authentication process with a Microsoft Live account and a managed Azure Active Directory account. In this post, we will take a look at the differences between the two processes.
Both processes start off with an OAuth authorization request initiated by Azure for an authorization code and an id token. The request does not differ between the two account types.
The processes continues with home realm discovery using the same query string. The results of the query give us the first differences between the process for a Microsoft Live and managed Azure Active Directory account.
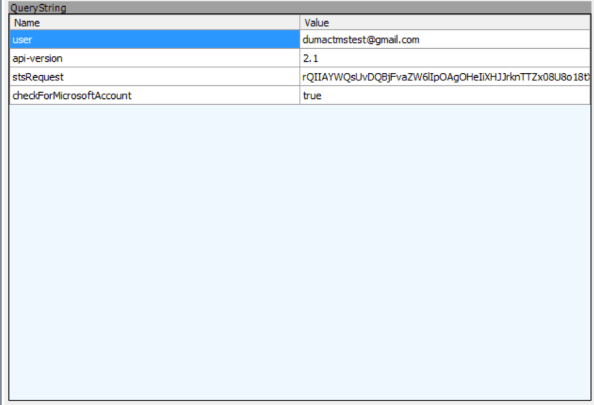
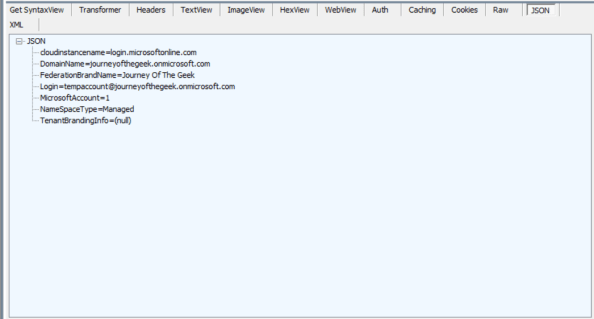
Take a minute and look at the differences between the two responses in the screenshots above. These are key to why the managed Azure Active Directory authentication didn’t require a redirect to another entity like the Microsoft Live account did.
You’ll notice that the managed Azure Active Directory authentication is lacking the AuthURI and federation_protocol attributes. These two attributes are required for the Microsoft Live account because Azure Active Directory doesn’t have the necessary information to authenticate the Microsoft Live account and has had a trust established where it now trusts Microsoft Live to authenticate the user. After Microsoft Live authenticates the user, it delivers the user a security token containing claims about the user. Azure Active Directory trusts the security token because it has been digitally signed by Microsoft Live’s security token service. What does this mean? It means Microsoft Live has been federated with the security token service behind Microsoft Azure.
With a managed account, Azure Active Directory has the necessary information to authenticate the user. The additional redirect is not necessary.
Some other small but interesting differences are the lack of the ConsumerDomain attribute in the managed Azure AD flow and the different values present in the MicrosoftAccount and NameSpaceType attributes. We see that when we use a Microsoft Live account, the MicrosoftAccount has a value of 0. Now we understand what that attribute and value mean.
Let’s move on to the identity token. There are a number of claims present in the managed Azure AD identity token that are not present in the Microsoft Live identity token. The family_name, given_name, name, oid, and upn claims are pulled from the Azure AD instance and included within the token. The altsecid seems to be unique to Microsoft Live, but I will be curious to see if that claim appears when an alternate login ID is used with a non-managed Azure AD account. Additionally, the idp claim is lacking from the managed Azure AD token since Azure AD directly authenticated the user.
I’ve included a Visio below which outlines the two processes and how they differ. I hope this post helps and I will be back with some more deep dives and helpful tips for your Azure Active Directory needs.