Hello again. Today I will continue this series by examining the GUI options available within Microsoft’s Azure offerings to provision new user accounts. I am going to focus on member user objects and not guests for this series.
There are four native GUI options available that can be used to provision new user accounts in Azure Active Directory.
- Office 365 Administration Center
- Azure Management Portal
- Azure Portal
- ADUC/ADAC then synchronization to Azure AD
I’ll start with the Office 365 Admin Center. The Office 365 Administration Center is where most business will find themselves provisioning user accounts due to the popularity of the products under the Office 365 umbrella. The Admin Center provides an interface that is sleek and simple to navigate. The simplicity comes with a price. Administration of many aspects of Azure AD must be done outside of the Admin Center. This registering custom applications and applications from the application gallery, creation of additional directories such as B2C directories, B2B imports, and much more. Microsoft seemingly intends this interface to be business friendly administration endpoint for the Office 365 suite and rightfully assumes the consumers of this endpoint need simplicity.
I’ll now create a new user account. We first need navigate and login to the Office 365 portal. After the user authenticates the Office 365 home page that lists out the various applications the user has access to. I’ll next click on the Admin icon to enter the Admin Center. Next I will navigate to the Users section and select the Active Users section. This will bring us up a listing of the users currently in the Azure AD tenant associated with the Office 365 subscription.

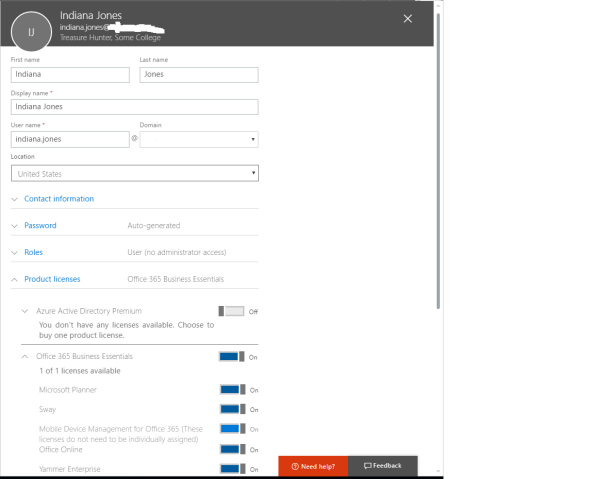
When I hit the Add User button a new blade opens where the key components of the user’s account can be configured. This includes the first name, last name, user name and the like as seen in the screenshot below.
Let’s take some time to dig through the remaining sections.
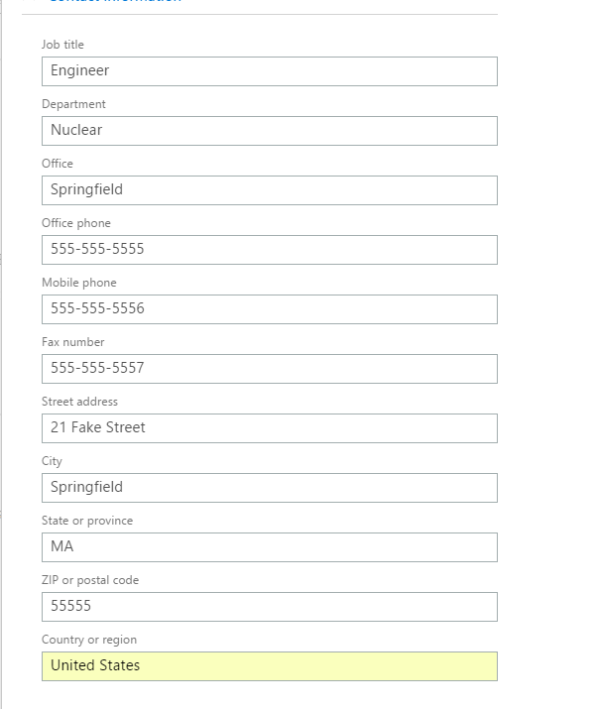
First up is the contact information section. On-premise Active Directory administrators will recognize these fields from the various tabs in ADUC.
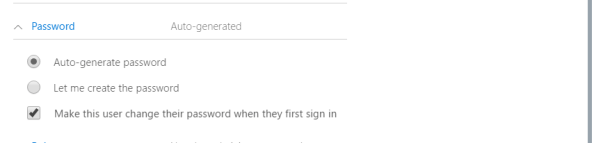
Next up is the password section. Here I have the option of creating a password or auto-generating a password and turning on or off the enforcement of a password change at first sign-in. I don’t recall there being an option to create a password a few months back when I was playing with the Admin Center, but that is one of the many lovely aspects of SaaS, continuous change and improvement.
Next up is the Roles section. Here there is an option to assign the user to the standard Azure AD roles or Office 365 roles. You can read more about these roles here.

Finally, the Licenses section allows for assignment of Azure AD and Office 365 licenses to the user account.

After the user is created it can be modified by clicking on the user object. Contact information about the user, membership into Azure AD groups, MFA enforcement, and product specific settings for the user can be modified in this blade.

The restoration of deleted users is simple and quick via the Deleted Users section. If only Microsoft had made it this easy in the old days of on-premises Active Directory prior to the Active Directory Administration Center.

Users can also be added in bulk by uploading a CSV file by hitting the More button in the Active Users section.

The Office 365 Admin Center interface is sleek and simple, perfect for a business user or Tier 1 support staff. So what’s the problem? No matter how simple the interface, it’s another process and interface staff need to learn. There is also no way to technically enforce standards for data input. What if what user puts MA and another puts Massachusetts? What about a user who misspells accountant in the job title field? Human error and lack of standardization can make for some nasty operational headaches, not to mention security risks. If an organization wants to limit the new processes and interfaces its staff needs to learn (because really, where is the business value in that?) as well as making sure the data about a user is standardized and correct, making these changes programmatically is the way to go.
In my next post I’ll cover both the Azure Management Portal and the Azure Portal.





